Why Are Organizations Embracing Multi-Cloud Strategies?
Organizations are really getting into multi-cloud these days. Instead of sticking with just one cloud provider, they’re using a mix of platforms like Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP). This big shift is happening because it offers some pretty great benefits that help businesses meet their current needs and prepare for the future.
One of the main reasons companies go multi-cloud is to avoid getting stuck with a single vendor. If you’re tied to just one provider, you might find yourself limited in terms of flexibility, how much you can negotiate on price, and even what services you can use. With a multi-cloud setup, you can spread out your work and data, so you’re not dependent on one vendor’s pricing or service limits. It’s not just about having a backup; it’s a smart move to get an edge on the competition. You get to pick the best services from each provider instead of settling for a single provider’s all-in-one package, which might not be perfect for everything. This way of choosing exactly what you need really changes how companies think about their cloud infrastructure.
Plus, putting your applications and data across different clouds makes things much more reliable and available. If one cloud goes down, your important operations can smoothly switch over to another, keeping things running and minimizing disruptions. This is super important for good disaster recovery planning, giving you a strong safety net against unexpected problems.
Multi-cloud also lets organizations pick services from different vendors, which can help them get better prices and lower their overall costs. This means companies can choose more affordable options after looking closely at costs versus performance, helping them avoid the downsides of one provider’s pricing structure. Beyond saving money directly, being more agile and flexible by using multiple cloud providers means businesses can find the best solutions for specific tasks. This helps them quickly adjust to new needs and encourages new ideas. That flexibility is key for trying out different services and technologies without being held back by one vendor’s system.
A multi-cloud strategy lets businesses customize their service choices to fit their unique operational needs. You can literally pick and choose specific services from different providers that best match your business goals. For example, a company might use GCP for its advanced Artificial Intelligence (AI) features while using AWS for its strong computing services. This ability to select “best-of-breed” services makes your cloud setup work perfectly for your specific tasks. Also, putting cloud services closer to your users by using different geographic regions from multiple providers can really cut down on delays, giving you better connections and a smoother experience for users. Edge computing helps even more by processing data closer to where it’s created, making applications respond faster. Finally, multi-cloud setups are becoming super important for meeting various rules and regulations. They let organizations store and process data in specific areas to follow data sovereignty laws and other requirements more easily.
Moving to multi-cloud isn’t just a technical choice; it’s a strategic one. It’s all about getting more control, making things more resilient, and staying competitive in today’s digital world. Here’s a quick look at the main benefits and challenges of going multi-cloud:
| Aspect | Benefits | Challenges |
|---|---|---|
| Strategic | Avoids Vendor Lock-in, Tailored Service Selection, More Agility/Flexibility | More Complex, Integration Issues, Need for Skilled People, Slower Rollouts |
| Operational | Better Reliability/Redundancy, Less Latency | Performance Bottlenecks, Network Delays/Bandwidth, Security Worries, Cost Management |
| Compliance | Helps Meet Regulations | Policies Can Get Messy |
What Challenges Does Multi-Cloud Introduce?
While multi-cloud offers some great advantages, it’s not without its tricky parts. Setting up and running a multi-cloud environment brings a whole new set of challenges that organizations really need to think about to get the most out of it.
Managing multiple cloud platforms naturally makes things more complicated, both in how you design your systems and how you run them. This is because each cloud provider has its own interfaces, rules, and ways of doing things. Keeping everything running smoothly and consistently across these different environments takes careful planning and coordination. This added complexity can also mean it takes longer to get things up and running and to deploy new features across different systems if you don’t have the right tools and strategy.
Security becomes a bigger concern in a multi-cloud setup. When your operations are spread out, there are more places for attacks to happen, and your security rules can get fragmented if you’re not careful. It’s really important to make sure you have strong and consistent security across all platforms, including using “Zero Trust” models where everyone accessing network resources needs to be verified. There’s also a higher risk of “Shadow IT,” which is when people use unauthorized cloud services.
Making sure data and workflows move smoothly across different cloud platforms is a big hurdle. You need to ensure that different systems and clouds can work together easily (interoperability) and that your data stays accurate and reliable across all environments. This calls for a smart approach to how you manage data and deploy applications across these diverse setups.
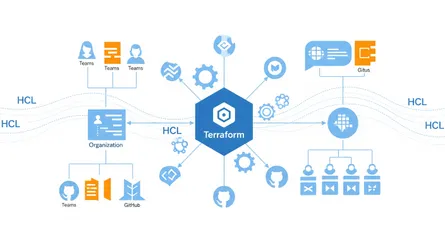
The complexity of multi-cloud systems means you need specialized and well-trained people. Understanding the ins and outs of different cloud platforms and managing them effectively requires a lot of expertise and experience. The learning curve for new tools and processes can be steep, especially if your teams aren’t strong in developer skills. The constant mention of needing skilled people tells us that human talent is a huge, often overlooked, challenge in adopting multi-cloud. It’s not just about finding folks with specific cloud certifications; it’s about building teams that can handle the challenges of getting different systems to work together. So, if you’re going multi-cloud, you’ll need to invest a lot in training your current teams or hiring new talent. And when you pick Infrastructure as Code (IaC) tools, think about how well they fit with your team’s current programming skills to make that learning curve easier.
Working across multiple clouds can also lead to slower network speeds and more bandwidth use, which can affect how well things perform and how users experience your services, especially when you need real-time data processing and quick responses. When you’re designing your systems, you really need to consider traffic between clouds, caching layers, and any potential delays if one system needs to take over for another.
While multi-cloud strategies promise to save you money, they also bring challenges in managing those costs. Unpredictable expenses and the need for smart financial operations (FinOps) to track usage and allocate costs across providers are common issues. This shows that multi-cloud doesn’t automatically save you money; it only does if you manage it well. The real cost goes beyond just computing resources; it includes the effort of managing complexity, investing in skilled people, and getting specialized tools. So, companies need to invest in strong FinOps practices and automation tools right from the start to truly get the cost benefits of multi-cloud, instead of just assuming it’ll happen. Without this proactive approach, the complexity can quickly eat away at any potential savings.
How Does Infrastructure as Code (IaC) Revolutionize Cloud Management?
When you’re dealing with all that multi-cloud complexity, Infrastructure as Code (IaC) really steps up as a game-changer. It completely changes how organizations manage and set up their IT resources. By treating infrastructure configurations like software, IaC brings amazing levels of automation, consistency, and scalability to today’s IT environments.
IaC is basically about managing and setting up computer data centers using machine-readable files. It replaces all the manual work you used to do for IT resource management and provisioning by simple lines of code. This approach has become super popular as systems get more complex, because trying to configure things manually just doesn’t cut it anymore.
Here are the main ideas behind IaC:
- Version Control: Just like with application code, your infrastructure code should live in a version control system, like Git. This lets your team keep track of changes over time, see who changed what and why, allows multiple people to work on it at once, and makes it easy to go back to a stable version of your infrastructure if something goes wrong.
- Idempotency: IaC scripts are designed to be “idempotent.” This means if you run them multiple times, you’ll get the same result as running them just once. For example, if a script is supposed to create a virtual machine (VM), running it again won’t create a duplicate VM; it’ll just see that the VM is already there and do nothing. This keeps things consistent and prevents accidental changes.
- Automation and Orchestration: At its heart, IaC turns your infrastructure into code, which means you can automate its entire life cycle. This includes setting up, configuring, updating, and even getting rid of resources. Orchestration takes automation a step further by coordinating many automated tasks, making complex deployments much smoother.
- Consistency and Repeatability: IaC helps keep things consistent across different environments, like development, testing, and production. You use the same code to deploy infrastructure everywhere, which cuts down on environment-specific problems and makes things reliable at scale. This consistency also means you can rebuild entire environments from scratch with confidence, which is incredibly useful for testing, fixing problems, and recovering from disasters.
The benefits of using IaC are huge. It makes things much faster and more consistent, cutting deployment times from hours to minutes without sacrificing security. This means you can make changes more quickly and ensure tasks are done reliably, since you’re not waiting on manual processes. By getting rid of human errors that come from manual configurations, IaC significantly reduces mistakes and makes infrastructure deployments more consistent. This reliability in setting up infrastructure lets developers focus more on building applications, because they can write infrastructure code once and reuse it many times, thus, saving time and effort. IaC can also lower management overhead by removing the need for many administrative roles focused on managing different hardware and software layers, freeing up people for more important tasks. Plus, IaC makes security better by moving from just checking things after they’re done to actively enforcing rules. IaC templates can include compliance requirements and security checks, looking for vulnerabilities before you even set things up and even automatically stopping infrastructure that doesn’t follow best practices.
Here’s a simple example of what IaC might look like, defining a basic cloud server:
# This is a generic IaC example, showing how you define infrastructure as code.# The exact syntax would vary depending on the IaC tool (e.g., Terraform, CloudFormation).
# Define a virtual serverresource "server" "web_server" { name = "my-web-server" region = "us-east-1" instance_type = "t2.micro" image_id = "ami-0abcdef1234567890" # Example AMI ID tags = { Environment = "Development" Project = "BlogPost" }}
# Define a network security group (firewall rules)resource "security_group" "web_server_sg" { name = "web-server-security-group" description = "Allow HTTP and SSH access"
ingress { from_port = 80 to_port = 80 protocol = "tcp" cidr_blocks = ["0.0.0.0/0"] # Allow HTTP from anywhere }
ingress { from_port = 22 to_port = 22 protocol = "tcp" cidr_blocks = # Allow SSH only from your IP }}IaC also lets you use variables to make your code flexible and reusable. This means you can define common settings once and then use them across different parts of your infrastructure or for different environments (like development vs. production).
# This is a generic IaC example showing how to use variables and outputs.# Variables make your infrastructure code flexible and reusable.
variable "instance_type" { description = "The type of instance to deploy (e.g., t2.micro, m5.large)" type = string default = "t2.micro" # A default value if not specified}
variable "environment_tag" { description = "Tag for the environment (e.g., dev, prod)" type = string}
resource "server" "my_server" { name = "blog-server-${var.environment_tag}" # Using the environment_tag variable instance_type = var.instance_type # Using the instance_type variable #... other server configurations tags = { Environment = var.environment_tag }}
# Outputs let you easily retrieve information about your deployed infrastructure.output "server_name" { description = "The name of the deployed server" value = resource.server.my_server.name}To truly embrace multi-cloud with IaC, you’d define resources for different providers within your code. This conceptual example shows how you might define a virtual machine in AWS and a resource group in Azure, all within a single IaC approach:
# This is a conceptual multi-cloud IaC example.# It shows how you might define resources for different cloud providers# within a single Infrastructure as Code approach.
# AWS Virtual Machine Definitionresource "aws_instance" "my_aws_vm" { ami = "ami-0abcdef1234567890" # Example AWS AMI ID instance_type = "t2.micro" region = "us-east-1" tags = { Name = "MultiCloud-AWS-VM" Environment = "Development" }}
# Azure Resource Group Definitionresource "azurerm_resource_group" "my_azure_rg" { name = "MultiCloud-Azure-RG" location = "East US" # Azure region tags = { Environment = "Development" }}
# Note: The actual syntax and tool would vary (e.g., Terraform, Pulumi, CloudFormation).# This example is for illustrative purposes to show multi-cloud definition in IaC.When you need to make a change to your infrastructure, IaC makes it straightforward. You simply update the code, and the IaC tool figures out what needs to be done to reach the new desired state. Here’s a conceptual example of updating the web_server from t2.micro to t2.medium:
# This is a conceptual IaC update example.# We're updating the 'instance_type' of our 'web_server' from 't2.micro' to 't2.medium'.# The IaC tool will detect this change and apply only what's necessary.
# Define a virtual serverresource "server" "web_server" { name = "my-web-server" region = "us-east-1" instance_type = "t2.medium" # Changed from t2.micro image_id = "ami-0abcdef1234567890" tags = { Environment = "Development" Project = "BlogPost" }}
# The rest of the configuration (like the security group) remains the same.# The IaC tool's "idempotency" ensures only the instance type is modified,# not recreating the entire server or security group unnecessarily.Even with all its advantages, IaC does have some challenges. A big skill gap and potential resistance from teams can make it hard to adopt, especially since it requires a significant learning curve if teams aren’t used to coding languages like JSON, HCL, YAML, or Ruby. Older security tools and processes might not be enough for how dynamic IaC is, meaning you might need extra steps and new tools to set up safeguards and rules. Keeping an eye on IaC can also be tough, as tracking who sets up what, where, how often, and at what cost often needs additional, more dynamic tools beyond old-fashioned spreadsheets. Finally, while it’s helpful, IaC can get complicated for really large and intricate infrastructures, possibly needing advanced knowledge of the underlying technology.
IaC isn’t just a “nice-to-have” in a multi-cloud world; it’s absolutely essential for making things efficient, secure, and scalable across different cloud environments. The benefits of IaC, like consistency, repeatability, and automation, directly tackle the main multi-cloud challenges, including complexity, integration problems, and messy policies. Without IaC, the inherent complexity of multi-cloud would probably overwhelm most organizations, turning a potentially chaotic mess into a controlled, well-managed landscape. This shift also means cloud professionals need new skills. The constant talk about a “skill gap” is directly linked to “coding language dependency”. This indicates a big change in what infrastructure professionals need to know: moving from manual configuration and graphical interface management to software development principles. Companies adopting IaC, especially in a multi-cloud setting, need to train their operations teams in software development practices or hire developers who understand infrastructure. This blurs the lines between traditional “Dev” and “Ops” roles and really strengthens the DevOps way of thinking.
| Aspect | Benefits | Challenges |
|---|---|---|
| Efficiency | Automation, Faster Deployments, Fewer Errors, Efficient Software Development, Less Management Overhead | Learning Curve/Skill Gap, Team Resistance, Monitoring Can Be Tricky |
| Quality | Consistency, Repeatability, Better Security | Security Checks Need Adapting, Complex for Big Systems |
| Control | Version Control, Track Changes, Easy Rollbacks | Initial Setup Costs |
What is Pulumi and How Does It Empower Developers?
Pulumi is a modern take on Infrastructure as Code. What makes it stand out is that it lets developers define and manage cloud infrastructure using programming languages they already know. This really makes it easier for developers to get started and smoothly brings infrastructure management into their existing software development routines.
Pulumi is an open-source IaC platform that lets DevOps teams and engineers use common programming languages like TypeScript, JavaScript, Python, Go,.NET, and Java to build, deploy, and manage cloud infrastructure like virtual machines, containers, and applications. Unlike older IaC tools that often rely on special languages (DSLs) or configuration files, Pulumi uses the full power of standard programming languages. This means developers can use regular coding practices like loops, functions, and if-then statements to create flexible and reusable configurations for their infrastructure, just like they would for their application code.
For example, you can use a simple loop in Python with Pulumi to create multiple similar resources, which is something you’d typically do in application development:
import pulumiimport pulumi_aws as aws
# Define a list of bucket names we want to createbucket_names = ["my-app-bucket-dev", "my-app-bucket-staging", "my-app-bucket-prod"]
# Loop through the list and create an S3 bucket for each namefor name in bucket_names: bucket = aws.s3.Bucket(name, bucket=name, # The actual bucket name in S3 acl="private", tags={ "Environment": name.split('-')[-1].capitalize(), # Tag based on environment "Project": "PulumiBlogLoop" }) pulumi.export(f"{name}_id", bucket.id) # Export each bucket's IDHere’s a simple Pulumi example in Python to create an AWS S3 bucket:
import pulumiimport pulumi_aws as aws
# Create an AWS S3 bucket# This bucket will store objects and is configured for private access.bucket = aws.s3.Bucket("my-pulumi-bucket", acl="private", # Access Control List: "private" means only the owner can access tags={ # Tags help organize and identify your resources "Environment": "Development", "Project": "PulumiBlog" })
# Export the name of the bucket# This makes the bucket name easily accessible after deployment.pulumi.export("bucket_name", bucket.id)To show Pulumi’s multi-cloud capabilities, here’s an example in TypeScript that creates an Azure Resource Group. Notice how the code structure remains familiar, even though it’s targeting a different cloud provider.
import * as azure_native from '@pulumi/azure-native';import * as pulumi from '@pulumi/pulumi';
// Create an Azure Resource Group// Resource Groups are logical containers for Azure resources.const resourceGroup = new azure_native.resources.ResourceGroup('my-azure-rg', { resourceGroupName: 'pulumi-blog-rg', // Name of the resource group location: 'EastUS', // Azure region for the resource group tags: { // Tags for organization Environment: 'Development', Project: 'PulumiBlog', },});
// Export the name of the resource grouppulumi.export('resourceGroupName', resourceGroup.name);Pulumi’s main strength is its support for many languages, giving engineers the freedom to pick the language they’re most comfortable with. This flexibility means you don’t have to learn special languages, which really cuts down on the time it takes to get started with new tools. Pulumi supports the whole infrastructure life cycle, including setting up, updating, and deleting resources, making sure things are consistent across different environments. Its Dynamic Provider feature lets you define and manage custom resources that aren’t directly supported by an existing Pulumi provider. This means you can create custom logic for pretty much any platform. Pulumi also encourages reusing code through its Pulumi Packages, letting developers define infrastructure building blocks and share them across teams. This helps keep things consistent and avoids doing the same work twice. By using the strong type checking features of the languages it supports, Pulumi helps prevent errors during deployment, offering a level of security and reliability you don’t always find in tools that use special languages. It also gives you great support in your code editor, with features like autocomplete and error checking, making the developer experience better. For handling sensitive information, Pulumi has strong built-in support through Pulumi ESC (Environment, Secrets, and Configuration), which encrypts secrets both when they’re moving around and when they’re stored. It also works with various external secret stores. What’s more, Pulumi automatically manages your infrastructure’s state, storing it securely in the Pulumi Cloud by default, with built-in state locking and encryption. You can also choose to use your own storage like AWS S3 or Azure Blob Storage. Pulumi also gives you real-time feedback by showing you changes before they’re deployed, which helps you avoid potential problems and make better decisions.
Pulumi excels in multi-cloud setups, working with major cloud providers like AWS, Azure, Google Cloud, and over 150 others. This means you can manage infrastructure across these different environments using programming languages you already know. This capability is really important for avoiding vendor lock-in and staying flexible across different cloud systems.
For organizations, Pulumi offers big advantages. By using familiar programming languages and software development methods, it helps developers write infrastructure code more efficiently, leading to faster development cycles and getting products to market quicker. Pulumi’s “infrastructure as software” approach improves teamwork between development, operations, and security teams through shared code repositories, code reviews, and automated testing. Developers get fine-grained control over infrastructure configurations, letting them customize resources for specific needs, which helps optimize performance, cost, and security. Importantly, by hiding the cloud provider-specific details, Pulumi reduces the risk of vendor lock-in, making it easier for organizations to switch providers or adopt a multi-cloud strategy with minimal hassle.
The core innovation of Pulumi, using general-purpose programming languages, directly addresses the skill gap often found in IaC by making infrastructure management accessible to a broader pool of software developers who already know these languages. This suggests that the future of IaC is becoming more developer-focused, making true DevOps possible by letting the same teams and skills manage both application code and the underlying infrastructure. This leads to more connected development processes and potentially faster innovation. Also, while some IaC tools let you manage state yourself, Pulumi’s default to a managed service for state isn’t just convenient. It solves big operational problems like managing transactional state, locking state for multiple users, keeping a full deployment history, and encrypting state. This takes a lot of complexity and risk off your plate, especially in team environments. The trend toward managed services for IaC state shows that people are realizing state management is a complex, critical part of automating infrastructure that, if handled poorly, can lead to outages and security breaches. Relying on a managed service lets organizations focus on their main business instead of dealing with infrastructure plumbing.
What is Crossplane and Why is Kubernetes Its Native Home?
Crossplane has a unique way of doing Infrastructure as Code: it extends the Kubernetes control plane itself to manage external cloud infrastructure. This basically turns Kubernetes into a “universal control plane,” letting organizations set up and manage resources across many cloud providers using the Kubernetes-native tools and processes they’re already familiar with.
Crossplane is an open-source Kubernetes add-on and cloud-native control plane that lets organizations manage and set up infrastructure across multiple cloud providers using Kubernetes-native APIs. It treats infrastructure like Kubernetes resources, so teams can define, deploy, and manage infrastructure using declarative configurations, just like they manage applications within Kubernetes. The project started at Upbound in 2018 and later joined the Cloud Native Computing Foundation (CNCF) in 2020, which shows its strong connection to cloud-native ideas.
Crossplane’s main strength is its Kubernetes-native approach. It uses Kubernetes concepts like Custom Resource Definitions (CRDs) and controllers to really expand Kubernetes’ ability to manage infrastructure resources. This means you can manage external resources, like servers and applications that aren’t traditionally part of a Kubernetes cluster, in the same way you manage pods and nodes. The core of Crossplane’s multi-cloud capabilities are its Providers. These are like plugins that let Crossplane talk to specific cloud services (like AWS, Azure, GCP) or other external systems. Each provider handles the logic needed to communicate with a particular cloud platform, which makes it easy to add new features to Crossplane.
A key feature is Compositions, also called Composite Resource Definitions (XRDs). These are high-level blueprints that define reusable infrastructure templates. By using compositions, platform teams can give developers simpler ways to request infrastructure, shielding them from the complex cloud details and making sure everyone follows best practices, uses cost-effective setups, and keeps things consistent across different environments and teams. This turns a Kubernetes cluster into a central control point for managing not just resources inside the cluster but also external cloud services, making the management experience consistent for both applications and infrastructure. Crossplane also works perfectly with GitOps workflows, letting you manage infrastructure configurations using version control systems. This makes it easier to track changes, improves teamwork through familiar code review processes, and ensures your deployed infrastructure always matches what’s defined in your repository. Plus, Crossplane enables policy-driven infrastructure setup and governance by integrating Kubernetes-native Role-Based Access Control (RBAC) and letting you embed policies within compositions.
Here’s a simple Crossplane example in YAML to create an AWS S3 bucket:
# This is a Crossplane example in YAML, defining an AWS S3 bucket.# Crossplane uses Kubernetes Custom Resource Definitions (CRDs) to represent cloud resources.
apiVersion: s3.aws.upbound.io/v1beta1 # API version for AWS S3 resources in Crossplanekind: Bucket # The kind of resource we want to create: an S3 Bucketmetadata: name: my-crossplane-bucket # A unique name for our bucketspec: forProvider: # These are the provider-specific configurations for the S3 bucket region: us-east-1 # The AWS region where the bucket will be created acl: private # Access Control List: "private" means only the owner can access tags: # Tags help organize and identify your resources Environment: Development Project: CrossplaneBlog providerConfigRef: # Reference to the Crossplane ProviderConfig, which holds AWS credentials name: default # Assumes you have a ProviderConfig named 'default' set up for AWSTo illustrate Crossplane’s powerful abstraction capabilities, here’s a conceptual example of a CompositeResourceDefinition (XRD) for a “ManagedDatabase.” This XRD defines a high-level database concept that platform teams can expose to developers, hiding the underlying cloud-specific details.
# This is a conceptual Crossplane CompositeResourceDefinition (XRD) example.# It defines a high-level "ManagedDatabase" that abstracts away cloud-specific details.# Platform teams create XRDs to offer simplified, reusable infrastructure blueprints.
apiVersion: apiextensions.crossplane.io/v1 # API version for Crossplane's API extensionskind: CompositeResourceDefinition # Defines a new kind of composite resourcemetadata: name: manageddatabases.example.com # The name of our new composite resourcespec: group: example.com # The API group for this composite resource names: kind: ManagedDatabase # The user-friendly name for this resource plural: manageddatabases # The plural form for kubectl commands versions: - name: v1alpha1 # Version of this API served: true referenceable: true schema: openAPIV3Schema: type: object properties: spec: type: object properties: parameters: # Parameters that developers can specify type: object properties: storageGB: type: integer description: 'Desired storage in GB.' engine: type: string description: 'Database engine (e.g., PostgreSQL, MySQL).' version: type: string description: 'Database engine version.' required: - parameters # This is where the magic happens: compositions define how this abstract # ManagedDatabase maps to actual cloud resources (e.g., AWS RDS, Azure Database). # The actual composition logic would be defined in a separate Composition resource.Once a platform team defines an XRD like ManagedDatabase, application developers can then “claim” an instance of that database using a simpler DatabaseClaim resource. This hides the complexity of the underlying cloud provider and specific database service.
# This is a conceptual Crossplane Claim example.# Developers use Claims to request infrastructure defined by platform teams.# This claim requests a "ManagedDatabase" instance.
apiVersion: example.com/v1alpha1 # Matches the group and version of the ManagedDatabase XRDkind: DatabaseClaim # The kind of claim, as defined in the XRD's claimNamesmetadata: name: my-app-db-claim # A unique name for this specific database instancespec: compositionSelector: # Optional: if there are multiple ways to fulfill the ManagedDatabase matchLabels: environment: development # Selects a composition optimized for development parameters: # Parameters passed to the ManagedDatabase storageGB: 50 engine: PostgreSQL version: '14' # The actual connection details (e.g., host, port, credentials) would be # provisioned by Crossplane and typically stored in a Kubernetes Secret # that the application can then consume.Crossplane excels in multi-cloud environments by providing a consistent way to manage resources across different providers (AWS, Azure, GCP, Alibaba Cloud) using a unified Kubernetes interface. This uniformity simplifies operations and reduces configuration errors. It helps you avoid vendor lock-in by offering a consistent way to interact with cloud services, no matter which cloud platform you’re using.
For organizations, Crossplane offers unified infrastructure management by bringing together the management of cloud resources and applications under one Kubernetes interface. This makes self-service infrastructure possible, where platform engineering teams can create portals that let developers set up pre-approved environments without manual help. Crossplane also makes it easier to move workloads around by hiding the specific details of underlying cloud provider APIs, so applications and configurations can move between clouds with minimal changes. Through its continuous reconciliation model, Crossplane automatically finds and fixes any “configuration drift,” making sure the actual state always matches the desired state. Finally, it helps with cost management and FinOps by making consistent resource tagging possible for accurate cost tracking and by working with cloud-native cost management tools, which leads to better FinOps practices.
Crossplane’s main idea of extending Kubernetes’ control plane means a big change: Kubernetes isn’t just for orchestrating containers anymore. It’s becoming the go-to system for managing all cloud resources, both external and internal. For organizations that are heavily invested in Kubernetes, Crossplane offers a way to bring their entire cloud operational model together, simplifying tools and using existing Kubernetes expertise. This can lead to much more efficient operations and a more unified “cloud-native” experience. Also, Crossplane’s compositions and self-service provisioning capabilities point to a bigger trend in platform engineering: building Internal Developer Platforms (IDPs) that hide cloud complexity from application developers. Developers can use high-level “golden paths” without needing deep cloud-specific knowledge. This makes Crossplane a powerful tool for platform teams to become “product owners” of their internal cloud infrastructure, offering curated, compliant, and easy-to-use infrastructure services to their internal developer customers, thereby shifting the burden of cloud complexity from individual development teams to a specialized platform team.
Pulumi vs. Crossplane: Which IaC Tool Fits Your Strategy?
While both Pulumi and Crossplane are strong Infrastructure as Code tools designed to handle multi-cloud environments, they approach the problem from very different angles. Understanding these differences is key to picking the right tool that fits your organization’s current tech setup, team skills, and overall goals.
Pulumi’s main idea is IaC that’s centered around programming languages. It brings infrastructure management into the familiar world of general-purpose programming languages like Python, TypeScript, Go,.NET, and Java. This lets developers use their existing coding skills to define and deploy infrastructure, making IaC a closer part of their usual development process. On the other hand, Crossplane’s main idea is a Kubernetes-native control plane. It extends Kubernetes to act as a control plane for infrastructure. Crossplane uses Kubernetes Custom Resource Definitions (CRDs) and the Kubernetes API to manage cloud resources, which makes infrastructure management smooth for teams already familiar with Kubernetes.
What Are the Best Practices for Multi-Cloud IaC Success?
Setting up multi-cloud Infrastructure as Code with tools like Pulumi and Crossplane needs more than just technical know-how. It requires a smart approach focused on best practices to get the most out of efficiency, security, cost control, and the developer experience.
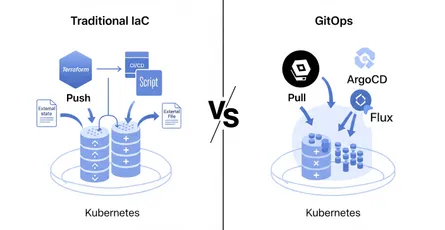
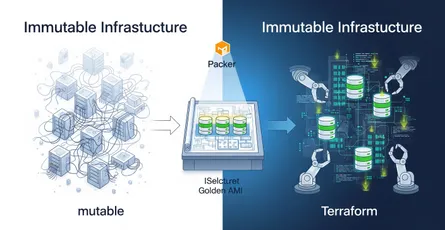
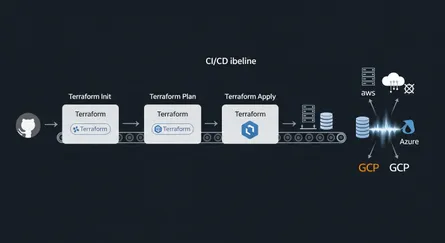
Basic IaC practices are super important. You should treat infrastructure code just like application code. This means all your IaC templates need to be stored in Git repositories so you can track changes, roll back errors, and work together effectively as a team. Setting up rules for branch protection and requiring pull requests for all infrastructure changes ensures that deployments are controlled and reviewed. Automating deployments through CI/CD pipelines (like Jenkins, GitLab CI, GitHub Actions) is crucial to kick off infrastructure updates whenever code is committed. Along with automation, you need to set up automated testing (unit, integration, and end-to-end) to check your infrastructure code before it’s deployed. This catches misconfigurations early in the development process. Also, break down complex infrastructure into reusable modules or components. This modular approach makes things easier to maintain and lets teams build complex environments from pre-tested building blocks. Putting documentation right into your IaC files ensures it stays up-to-date with code changes. Finally, embracing “immutable infrastructure,” where servers are treated as disposable resources and new instances with updates are deployed instead of patching existing ones, really cuts down on downtime and simplifies rollbacks.
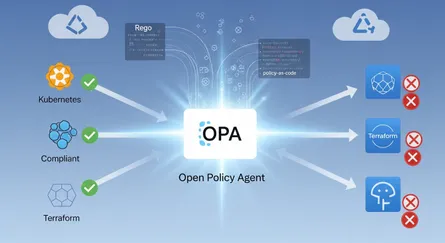
For multi-cloud and security-specific practices, being proactive is essential. You need to build security best practices and safeguards directly into your IaC process. This means integrating security scanning tools (like Checkov, Terrascan) into your CI/CD pipelines and using “policy-as-code” tools like Open Policy Agent (OPA) to enforce security rules and compliance requirements (like SOC2, HIPAA, PCI DSS, ISO27001, CIS). This “shift-left” approach to security makes sure that non-compliant deployments are stopped right from the start. Adopting a Zero Trust security model, which requires verification for all resource access no matter where it comes from, is also critical. Centralized Identity and Access Management (IAM) is another cornerstone; unifying IAM across multiple clouds using common standards like SAML or OAuth helps avoid vendor lock-in and simplifies user management. Implementing Single Sign-On (SSO) and Multi-Factor Authentication (MFA) further strengthens access control.
Centralized monitoring and cost management (FinOps) are absolutely necessary. A single monitoring solution that gathers logs, metrics, and traces from all clouds makes troubleshooting easier and gives you real-time insights into performance. For cost management, adopting FinOps practices, standardizing provisioning with IaC templates, centralizing audit logging, applying consistent tagging and labeling across all providers, and enforcing least privilege access are key to optimizing spending. Finally, when picking cloud vendors, organizations need to have clear exit strategies. This means understanding termination conditions, help with moving data, and automatic renewal clauses to ensure smooth transitions if you ever need to switch.
The focus on better security and building security best practices into IaC pipelines shows a shift: security isn’t an afterthought anymore; it’s a built-in part of how you define your infrastructure. For multi-cloud environments, where there are more places for attacks and policies can get messy, IaC becomes the main way to ensure consistent security and compliance at scale. This makes security a shared responsibility across development, operations, and security teams. Many of these best practices, such as breaking things into modules, customizable templates, centralized monitoring, and policy-as-code, are key parts of platform engineering. This suggests that successfully adopting multi-cloud IaC naturally pushes organizations toward building internal platforms that hide complexity and offer self-service capabilities. Organizations aiming for multi-cloud IaC success will likely find themselves moving toward a “platform team” model, where a dedicated group focuses on building reusable, compliant, and secure infrastructure components that other development teams can easily use. This is a strategic organizational change driven by the technical demands of multi-cloud.
What’s Next for Multi-Cloud IaC?
The world of multi-cloud Infrastructure as Code is always changing, driven by new technologies and the growing demands of digital transformation. Several upcoming trends are set to shape how organizations manage their various cloud environments in the future.
Artificial Intelligence (AI) will play a bigger role in cloud security and automation. AI-driven insights will help automate security responses, spot unusual activity, optimize how resources are used, and predict potential problems across multi-cloud environments. Specifically, AI-driven insights will find old, unused infrastructure and help optimize costs, moving beyond just reacting to problems to actively making things better. This suggests that future multi-cloud IaC tools will increasingly include machine learning and AI features to provide autonomous infrastructure management, reducing manual work and maximizing efficiency and security, further empowering FinOps and platform engineering teams.
We’ll see more advanced cloud marketplaces and pricing models based on how much you use. The explosion of services and flexible pricing across cloud providers will continue, meaning we’ll need more sophisticated IaC tools that can quickly adapt to cost-performance analyses and take advantage of competitive offers. Growing concerns about data sovereignty and global political factors will increase the demand for “sovereign cloud” solutions, where data stays within specific national borders. This will significantly impact multi-cloud strategies and IaC requirements for compliance. The mention of sovereign cloud and data sovereignty laws highlights that technical decisions in multi-cloud are increasingly influenced by non-technical, geopolitical factors. This adds a layer of complexity beyond just technical considerations like performance or cost. Multi-cloud IaC strategies will need to include advanced policy-as-code capabilities that can enforce geographical data residency and compliance requirements, becoming a critical component for organizations operating in regulated industries or across diverse international jurisdictions.
The way cloud and edge computing come together will blur the lines between central data centers and distributed edge locations. Multi-cloud IaC will need to reach out and manage infrastructure across this whole spectrum, optimizing for less delay and localized processing. We might also see more highly specialized, industry-specific cloud solutions tailored to unique industry needs, like healthcare or finance. This will require IaC tools to work with these niche services while keeping multi-cloud consistency. Finally, the trend toward building Internal Developer Platforms (IDPs) will get even stronger, with IaC tools like Pulumi and Crossplane forming the backbone of these platforms. This will enable more self-service, standardization, and governance for developers. This ongoing evolution of platform engineering will be a key driver for multi-cloud IaC adoption and sophistication.
Frequently Asked Questions (FAQs)
This section answers common questions about multi-cloud IaC and the roles of Pulumi and Crossplane. We’ll give you clear and simple answers to help you understand these key concepts.
Vendor lock-in happens when an organization is basically forced to keep using a product or service from one provider because it would be too expensive or difficult to switch. In cloud computing, this occurs when a platform or service only works with other offerings from the same vendor. Multi-cloud strategies, made easier by IaC tools like Pulumi and Crossplane, directly address this by letting organizations deploy and manage workloads across many providers. By hiding provider-specific details (Pulumi) or giving you a unified control plane (Crossplane), these tools reduce your reliance on any single vendor, giving businesses more freedom and flexibility.
No, IaC and DevOps are related but they’re not the same thing. IaC is a core practice within DevOps. DevOps is a way of thinking and working that aims to bring software development (Dev) and IT operations (Ops) closer together. The goal is to speed up the software development life cycle and deliver high-quality software continuously. IaC helps make many DevOps principles possible by automating infrastructure setup, ensuring consistency, and allowing version control, which leads to faster deployments and better teamwork.
Yes, both Pulumi and Crossplane can manage on-premises infrastructure, often as part of a hybrid cloud strategy. Pulumi supports hybrid cloud/on-premises resources and can use dynamic providers for services you host yourself. Crossplane, as a Kubernetes-native control plane, can extend to on-prem environments and manage resources there, especially when integrated with Kubernetes clusters running on-premises.
Pulumi has strong built-in support for secrets management through Pulumi ESC (Environment, Secrets, and Configuration). It encrypts sensitive data both when it’s moving and when it’s stored, using Hardware Security Module (HSM)-based encryption. It can also pull and sync secrets from various external stores like HashiCorp Vault, AWS Secrets Manager, Azure Key Vault, and 1Password. Crossplane doesn’t have a dedicated secrets management service like Pulumi ESC, but it uses Kubernetes secrets for storing credentials (like cloud provider API keys). This means you can use standard Kubernetes secret management practices and integrations with external secret stores through Kubernetes operators.
Pulumi is great for teams with strong programming skills (Python, TypeScript, Go, etc.) because it uses familiar software development workflows. It makes the learning curve easier for developers who already know these languages. Crossplane needs deep Kubernetes knowledge, including familiarity with CRDs, controllers, and Kubernetes-native tools. It’s best for organizations already heavily invested in the Kubernetes ecosystem. If you use both tools together, you’ll need expertise in both areas, often requiring a specialized “platform engineering” team to manage the integration and abstraction layers. The choice between Pulumi and Crossplane really depends on your team’s existing expertise and whether your organization is Kubernetes-centric. This highlights that your operational model and current organizational strengths are most important, rather than one tool being objectively “better.” Organizations shouldn’t just evaluate IaC tools based on features, but primarily on how well they fit with their current operational model, team capabilities, and strategic commitment to a particular control plane (like Kubernetes). A mismatch can lead to a lot of friction and make adoption difficult.
Conclusion: Charting Your Course in the Multi-Cloud Landscape
Moving into multi-cloud environments isn’t really an option for many organizations anymore; it’s a must-do. This is because businesses need resilience, cost savings, and amazing flexibility. But this journey can be complicated, from managing different interfaces to making sure security and compliance are consistent across all platforms. Infrastructure as Code (IaC) is the essential foundation for navigating this complex landscape, turning manual, error-prone tasks into automated, repeatable processes.
Tools like Pulumi and Crossplane are at the forefront of multi-cloud IaC. Each offers unique strengths that fit different organizational needs. Pulumi empowers developers by letting them define infrastructure using programming languages they already know, smoothly bringing cloud management into their existing software development routines. This approach boosts productivity, teamwork, and gives you fine-grained control, making IaC accessible to more people. Crossplane, on the other hand, extends the power of Kubernetes, turning it into a universal control plane for managing all cloud resources through a unified, declarative API. This is perfect for Kubernetes-focused organizations looking to bring all their infrastructure management under one powerful orchestration layer, enabling self-service and strong policy enforcement.
The most forward-thinking organizations are even looking at combining Pulumi and Crossplane. They use Pulumi to set up foundational Kubernetes clusters across different clouds, and then use Crossplane to manage cloud services within those clusters. While this layered approach adds a new level of operational complexity, especially when debugging issues that span both tools, it unlocks incredible scalability, reproducibility, and policy-driven governance. It’s truly the cutting edge of platform engineering.
As the cloud ecosystem keeps changing rapidly, following multi-cloud IaC best practices – from strict version control and automated testing to building in security safeguards and adopting FinOps principles – will be crucial. The future of multi-cloud IaC promises even more automation and optimization through AI-driven insights, further blurring the lines between infrastructure and application development. By smartly adopting and integrating these powerful IaC tools, organizations can not only overcome the challenges of multi-cloud but also set themselves up for continuous innovation and a competitive edge in the dynamic digital world.
References
- What is vendor lock-in? | Vendor lock-in and cloud computing - Cloudflare, accessed on June 6, 2025, https://www.cloudflare.com/learning/cloud/what-is-vendor-lock-in/
- 16 Most Useful Infrastructure as Code (IaC) Tools for 2025 - Spacelift, accessed on June 6, 2025, https://spacelift.io/blog/infrastructure-as-code-tools
- Pulumi: A Modern Infrastructure as Code (IaC) Alternative to Terraform - Devtron, accessed on June 6, 2025, https://devtron.ai/blog/introduction-to-pulumi-a-modern-infrastructure-as-code-platform/
- Pulumi: Empowering Infrastructure Engineers with Real Programming Languages, accessed on June 6, 2025, https://dev.to/fajmayor/pulumi-empowering-infrastructure-engineers-with-real-programming-languages-kp1
- Terraform vs. Pulumi vs. Crossplane: Choosing the Right IaC Tool for Your Internal Developer Platform - DEV Community, accessed on June 6, 2025, https://dev.to/romulofrancas/terraform-vs-pulumi-vs-crossplane-choosing-the-right-iac-tool-for-your-internal-developer-3a95
- Modern Infrastructure as Code: OpenTofu vs. Crossplane vs. Pulumi - DEV Community, accessed on June 6, 2025, https://dev.to/shashankpai/modern-infrastructure-as-code-opentofu-vs-crossplane-vs-pulumi-3gih
- Crossplane | Pulumi Docs, accessed on June 6, 2025, https://www.pulumi.com/docs/iac/concepts/vs/crossplane/
- Revolutionizing Cloud Management: How Crossplane is Reshaping the Future of Infrastructure Management | Devoteam, accessed on June 6, 2025, https://www.devoteam.com/expert-view/revolutionizing-cloud-management-how-crossplane-is-reshaping-the-future-of-infrastructure-management/
- Platform Engineering Simplified: The Power of Crossplane’s Nested Abstractions, accessed on June 6, 2025, https://blog.upbound.io/platform-engineering-simplified
- Automating Cloud Provisioning Using Pulumi and Crossplane - ResearchGate, accessed on June 6, 2025, https://www.researchgate.net/publication/391015338_Automating_Cloud_Provisioning_Using_Pulumi_and_Crossplane